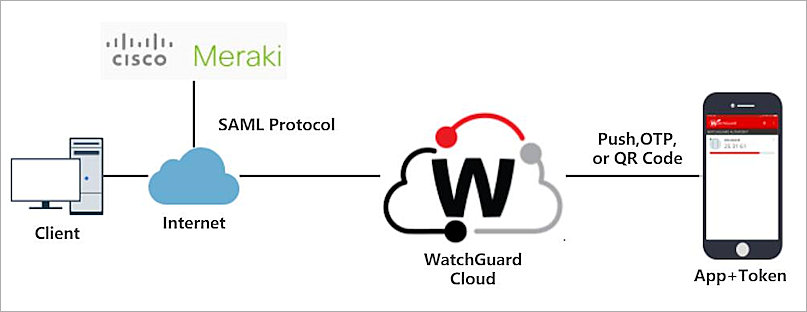
When using Meraki hosted authentication, VPN account/user name setting on client devices (e.g., PC or Mac) is the user email address entered in the Dashboard. Open Start Menu Search 'VPN' Click Change virtual private networks (VPN) From the VPN settings page, click Add a VPN connection. In the Add a VPN connection dialog. In order to participate in Auto VPN an MX device must register with the Meraki VPN registry. The VPN registry is a cloud-based system that stores data needed to connect all MX devices into an orchestrated VPN system. The VPN registry is always on and always updating in the case of a connection failure. Cisco Meraki uses the integrated Windows client for VPN connection (no Cisco client at this time). To be able to connect with simple AD user account credentials, along with a simple pre-shared key, the steps are very simple. After a few weeks going round-and-round with Meraki, we determined that.the Client VPN is working as intended. From a reasonably secure IPv4 public address to our client VPN address, it works perfectly. The problem comes that, when thrust into the 'real world', it fails in a wide variety of scenarios: IPv6 to IPv4 fails. Meraki VPN Client Setup. This short and sweet script will help with setting up the Windows VPN to use with Cisco Meraki firewall/routers. You can either run it raw or it can be included in your automation to deploy workstations at scale.
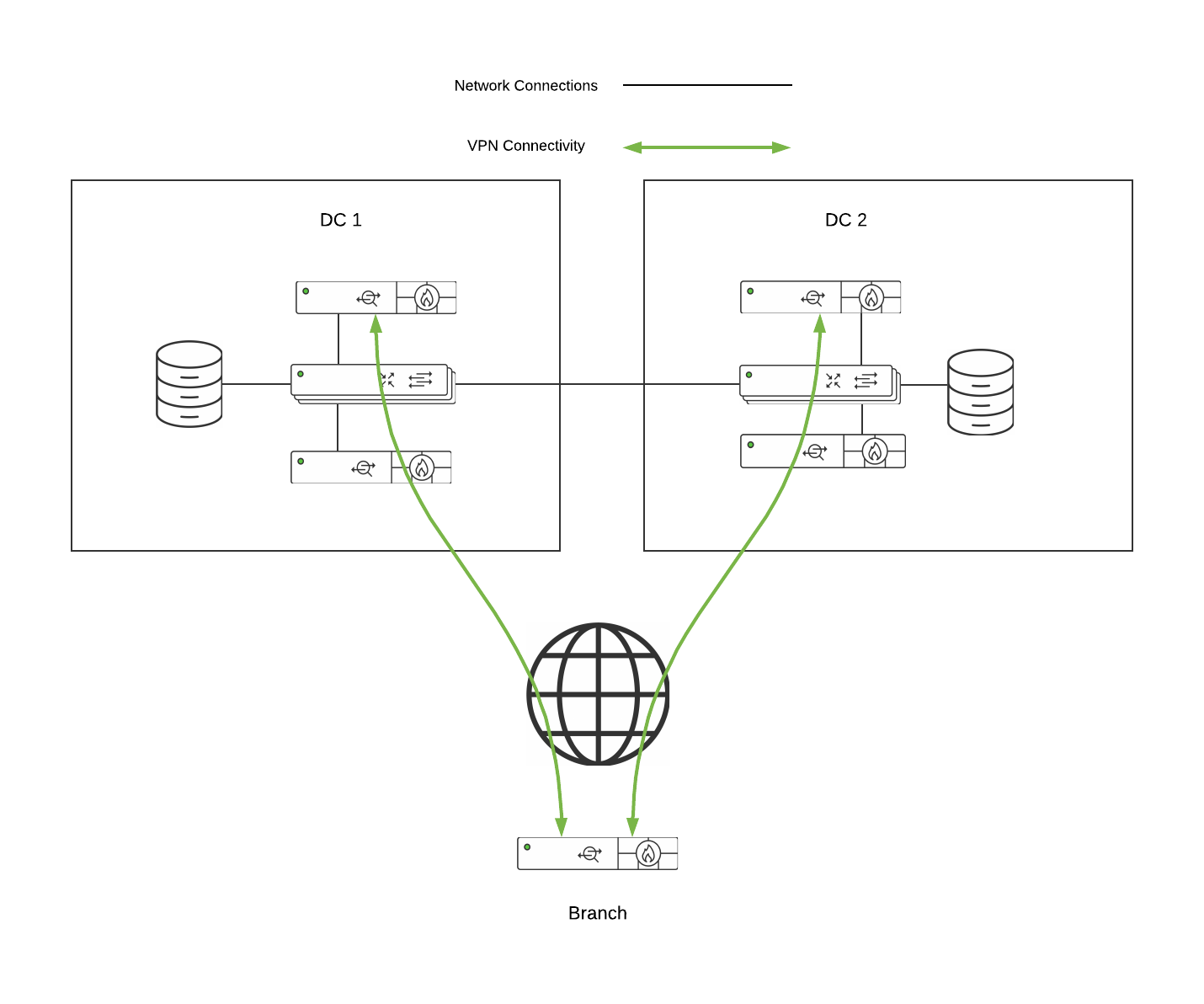
Setting up site-to-site VPN
Site-to-site VPN settings are accessible through the Security & SD-WAN > Configure > Site-to-site VPN page.
Type
There are three options for configuring the MX-Z's role in the Auto VPN topology:
- Off: The MX-Z device will not participate in site-to-site VPN.
- Hub (Mesh): The MX-Z device will establish VPN tunnels to all remote Meraki VPN peers that are also configured in this mode, as well as any MX-Z appliances in hub-and-spoke mode that have the MX-Z device configured as a hub.
- Spoke: This MX-Z device (spoke) will establish direct tunnels only to the specified remote MX-Z devices (hubs). Other spokes will be reachable via their respective hubs unless blocked by site-to-site firewall rules.
Hub Type
Exit Hubs
This option is only available if the MX-Z device is configured as a Hub. This option lets you designate the remote MX-Z device that is to receive all network traffic from the local MX-Z device. This creates a Full Tunnel configuration where all traffic destined for a default route is sent to the specified MX.
Security features over full-tunnel VPN
In a full tunnel topology, all security and content filtering must be performed on the full tunnel client. The Exit hub will not apply Content Filtering, IPS blocking, or Malware Scanning to traffic coming in over the VPN. However, IDS scanning will be performed for this traffic.
Spoke Type
Hubs
When an appliance is configured as a Spoke, multiple VPN Hubs can be configured for that appliance. In this configuration, the Spoke MX-Z device will send all site-to-site traffic to its configured VPN hubs.
Default Route
When configuring Hubs for a Spoke, there is an option to select a hub as being a Default route. If this option is selected, then that hub will be configured as a default route for the Spoke (0.0.0.0/0). Any traffic that is not sent to a configured VPN peer network, static route or local network will be sent to the default route. Multiple hubs can be selected as default routes. Hubs marked as default routes take priority in descending order (first priority at the top).
Configuring multiple VPN hubs
To add additional hubs, click the 'Add a hub' button just below the existing hub that is selected. Please note that only appliances in Mesh VPN mode can be hubs, so the number of Mesh VPN appliances in your Dashboard organization represents the maximum number of hubs that can be configured for any given appliance.
The order in which hubs are configured on this page is the hub priority. Hub priority is used to determine which hub to use if more than one VPN hub is advertising the same subnet. The uppermost hub that meets the following criteria will be used to reach that subnet.
A) Advertises the subnet
B) Currently reachable via VPN
Cisco Meraki Vpn
Hubs can be deleted by clicking on the grey 'X' to the right of the relevant hub under the Actions column. The hub priority list can be reordered by clicking and dragging the grey four-point arrow icon to the right of any hub in the list to move that hub up or down.
Tunneling
There are two tunneling modes available for MX-Z devices configured as a Spoke:
- Split tunnel (no default route): Send only site-to-site traffic, meaning that if a subnet is at a remote site, the traffic destined for that subnet is sent over the VPN. However, if traffic is destined for a network that is not in the VPN mesh (for example, traffic going to a public web service such as www.google.com), the traffic is not sent over the VPN. Instead, this traffic is routed using another available route, most commonly being sent directly to the Internet from the local MX-Z device. Split tunneling allows for the configuration of multiple hubs.
- Full tunnel (default route): The configured Exit hub(s) advertise a default route over Auto VPN to the spoke MX-Z device. Traffic destined for subnets that are not reachable through other routes will be sent over VPN to the Exit hub(s). Exit hubs' default routes will be prioritized in descending order.
Concentrator priority
The concentrator priority determines how appliances in Hub (Mesh) mode will reach subnets that are advertised from more than one Meraki VPN peer. Similarly to hub priorities, the uppermost concentrator in the list that meets the following criteria will be used for such a subnet.
A) Advertises the subnet
B) Currently reachable via VPN
It is important to note that concentrator priorities are used only by appliances in Meshmode. An appliance in Hub-and-Spoke mode will ignore the concentrator priorities and will use its hub priorities instead.
NAT Traversal
If the MX-Z device is behind a firewall or other NAT device, there are two options for establishing the VPN tunnel: Drivers navman nz port devices.
- Automatic: In the vast majority of cases, the MX-Z device can automatically establish site-to-site VPN connectivity to remote Meraki VPN peers even through a firewall or NAT device using a technique known as 'UDP hole punching'. This is the recommended (and default) option.
- Manual: Port forwarding: If the Automatic option does not work, you can use this option. When Manual: Port forwarding is enabled, Meraki VPN peers contact the MX-Z device using the specified public IP address and UDP port number. You will need to configure the upstream firewall to forward all incoming traffic on that UDP port to the IP address of the MX-Z device.
Make sure the port number you have chosen is not already used by another service. For example, do not use port 500 or 4500 as these are used for Client VPN and 3rd party VPN peer communication.
If you have multiple LAN subnets, you have the option to specify which VLANs and static routes participate in the VPN.
The same subnet can only be advertised from more than one appliance if all appliances advertising that subnet are in Passthrough or VPN Concentratormode. All subnets advertised from an appliance in Routed mode must be unique within the Auto VPN topology.
Subnets to which the MX-Z device has Static LAN routes can also be advertised over the VPN. If you choose to advertise a statically routed subnet over the VPN, ensure that the gateway device for each subnet is configured to route traffic for remote VPN subnets to the MX-Z device, in order to keep your routing symmetrical.
In full tunnel configurations when specifying a prefix to be part of a VPN, everything covered by that prefix will be allowed in the VPN. Therefore, subnets that overlap will cause traffic in a more specific subnet to be sent through the VPN, even if it is not configured to be included in the VPN. For example, if 10.0.0.0/16 is configured to be included in the VPN but 10.0.1.0/24 is not, traffic sourced from 10.0.1.50 will still be sent over the VPN.
VPN Subnet Translation
This feature is not enabled by default, please contact Meraki support to enable it.
Moreover, this feature is only supported for Auto VPN and is not intended to work with non-Meraki VPN peers.
In large distributed networks, multiple networks may have identical subnet scopes (i.e. overlapping subnets). Site-to-site VPN communication requires each site to have distinct and non-overlapping local subnets. In the event that multiple locations have the same local subnet, enable VPN subnet translation to translate the local subnet to a new subnet with the same number of addresses.
Subnet Translation Example

- Branch 1 local subnet: 192.168.31.0/24
- Branch 2 local subnet: 192.168.31.0/24 (identical!)
- Branch 1 translated subnet: 10.0.1.0/24
- Branch 2 translated subnet: 10.0.2.0/24
OSPF route advertisement
While the MX Security Appliance does not currently support full OSPF routing, OSPF can be used to advertise remote VPN subnets to a core switch or other routing device, avoiding the need to create static routes to those subnets. OSPF advertisement is only supported in VPN Concentrator mode.
Advertise remote routes: If this is set to Enabled, OSPF will be used to advertise remote VPN subnets as reachable via this concentrator.
Router ID: The OSPF Router ID that this concentrator will use to identify itself to neighbors
Area ID: The OSPF Area ID that this concentrator will use when sending route advertisements.
Cost: The route cost attached to all OSPF routes advertised from this concentrator.
Hello timer: How frequently the concentrator will send OSPF Hello packets. This should be the same across all devices in your OSPF topology.
Dead timer: How long the concentrator will wait to see Hello packets from a particular OSPF neighbor before considering that neighbor inactive
MD5 Authentication: If this is enabled, MD5 hashing will be used to authenticate potential OSPF neighbors. This ensures that no unauthorized devices are injecting OSPF routes into the network.
Authentication Key: The MD5 key number and passphrase. Both of these values must match between any devices that you wish to form an OSPF adjacency.
You can create Site-to-site VPN tunnels between a Security Appliance or a Teleworker Gateway and a Non-Meraki VPN endpoint device under the Non-Meraki VPN peers section on the Security & SD-WAN > Configure > Site-to-site VPN page. Simply click 'Add a peer' and enter the following information:
- A name for the remote device or VPN tunnel.
- What IKE version to use (IKEv1 or IKEv2)*
- The public IP address of the remote device.
- The Remote ID of the remote peer. This is an optional configuration and can be configured to the remote peer’s UserFQDN (e.g. user@domain.com), FQDN (e.g. www.example.com) or IPv4 address as needed.
- Which of these values you use is dependent upon your remote device. Please consult its documentation to learn what values it is capable of specifying as its remote ID, and how to configure them (e.g. crypto isakmp identity for ASA firewalls)
- The subnets behind the third-party device that you wish to connect to over the VPN. 0.0.0.0/0 can also be specified to define a default route to this peer.
Note that if an MX-Z device is configured with a default route (0.0.0.0/0) to a Non-Meraki VPN peer, traffic will not fail over to the WAN, even if the connection goes down.
- The IPsec policy to use.
- The preshared secret key (PSK).
- Availability settings to determine which appliances in your Dashboard Organization will connect to the peer.
*IKEv2 requires firmware version 15.12 or greater
NOTE For IKEv2
Meraki Appliances build IPsec tunnels by sending out a request with a single traffic selector that contains all of the expected local and remote subnets. Certain vendors may not support allowing more than one local and remote selector in a given IPsec tunnel (e.g. ASA 5500-X series firewalls running certain firmware releases); for such cases, please use IKEv1 instead.
An MX-Z device will not try to form a VPN tunnel to a non-Meraki peer if it does not have any local networks advertised.
IPsec policies
There are three preset IPsec policies available.
- Default: Uses the Meraki default IPsec settings for connection to a non-Meraki device
- AWS: Uses default settings for connecting to an Amazon VPC
- Azure: Uses default settings for connecting to a Microsoft Azure instance
If none of these presets are appropriate, the Custom option allows you to manually configure the IPsec policy parameters. These parameters are divided into Phase 1 and Phase 2.
Phase 1
- Encryption: Select between AES-128, AES-192, AES-256, and 3DES encryption
- Authentication: Select MD5, SHA1 or SHA256* authentication
- Diffie-Hellman group: Select between Diffie-Hellman (DH) groups 1, 2, and 5
- Lifetime (seconds): Enter the phase 1 lifetime in seconds
*SHA256 requires firmware version 15.12 or greater
Phase 2
- Encryption:Select between AES-128, AES-192, AES-256, and 3DES encryption (multiple options can be selected)
- Authentication:Select between MD5 and SHA1 authentication (both options can be selected)
- PFS group: Select the Off option to disable Perfect Forward Secrecy (PFS). Select group 1, 2, or 5 to enable PFS using that Diffie Hellman group.
- Lifetime (seconds): Enter the phase 2 lifetime in seconds
On May 8th 2018, changes were introduced to deprecate DES for encryption. Click here for more information.

Meraki Always On Vpn Login
NOTE: Please ensure the phase 2 lifetimes are equal on both ends of the tunnel whenever possible. While MX's can sometimes honor a shorter phase 2 lifetime if they're acting in response to build a tunnel, they cannot while serving as the initiator of the tunnel.
Peer availability
By default, a non-Meraki peer configuration applies to all MX-Z appliances in your Dashboard Organization. Since it is not always desirable for every appliance you control to form tunnels to a particular non-Meraki peer, the Availability column allows you to control which appliances within your Organization will connect to each peer. This control is based on network tags, which are labels you can apply to your Dashboard networks.
When 'All networks' is selected for a peer, all MX-Z appliances in the organization will connect to that peer. When a specific network tag or set of tags is selected, only networks that have one or more of the specified tags will connect to that peer.
More information on network tags can be found here.
VPN Firewall Rules
You can add firewall rules to control what traffic is allowed to pass through the VPN tunnel. These rules will apply to outbound VPN traffic to/from from all MX-Z appliances in the Organization that participate in site-to-site VPN. These rules are configured in the same manner as the Layer 3 firewall rules described on the Firewall Settings page of this documentation. Note that VPN Firewall rules will not apply to inbound traffic or to traffic that is not passing through the VPN.
-->Applies To: Windows Server (Semi-Annual Channel), Windows Server 2016, Windows 10
In this topic, you learn about the features and functionalities of Always On VPN. The following table is not an exhaustive list, however, it does include some of the most common features and functionalities used in remote access solutions.
Tip
Meraki Always On Vpn Download
If you currently use DirectAccess, we recommend that you investigate the Always On VPN functionality carefully to determine if it addresses all of your remote access needs before migrating from DirectAccess to Always On VPN.
| Functional area | Always On VPN |
|---|---|
| Seamless, transparent connectivity to the corporate network. | You can configure Always On VPN to support auto-triggering based on application launch or namespace resolution requests. Define using: |
| Use of a dedicated Infrastructure Tunnel to provide connectivity for users not signed into the corporate network. | You can achieve this functionality by using the Device Tunnel feature in the VPN profile. Note: Define using: |
| Use of manage-out to allow remote connectivity to clients from management systems located on the corporate network. | You can achieve this functionality by using the Device Tunnel feature in the VPN profile combined with configuring the VPN connection to dynamically register the IP addresses assigned to the VPN interface with internal DNS services. Note: Define using: |
| Fall back when clients are behind firewalls or proxy servers. | You can configure to fall back to SSTP (from IKEv2) by using the automatic tunnel/protocol type within the VPN profile. Note: Define using: |
| Support for end-to-edge access mode. | Always On VPN provides connectivity to corporate resources by using tunnel policies that require authentication and encryption until they reach the VPN gateway. By default, the tunnel sessions terminate at the VPN gateway, which also functions as the IKEv2 gateway, providing end-to-edge security. |
| Support for machine certificate authentication. | The IKEv2 protocol type available as part of the Always On VPN platform specifically supports the use of machine or computer certificates for VPN authentication. Note: Define using: |
| Use security groups to limit remote access functionality to specific clients. | You can configure Always On VPN to support granular authorization when using RADIUS, which includes the use of security groups to control VPN access. |
| Support for servers behind an edge firewall or NAT device. | Always On VPN gives you the ability to use protocols like IKEv2 and SSTP that fully support the use of a VPN gateway that is behind a NAT device or edge firewall. Note: |
| Ability to determine intranet connectivity when connected to the corporate network. | Trusted network detection provides the capability to detect corporate network connections, and it is based on an assessment of the connection-specific DNS suffix assigned to network interfaces and network profile. Define using: |
| Compliance using Network Access Protection (NAP). | The Always On VPN client can integrate with Azure conditional access to enforce MFA, device compliance, or a combination of both. When compliant with conditional access policies, Azure AD issues a short-lived (by default, 60 minutes) IPsec authentication certificate that the client can then use to authenticate to the VPN gateway. Device compliance takes advantage of Configuration Manager/Intune compliance policies, which can include the device health attestation state. At this time, Azure VPN conditional access provides the closest replacement to the existing NAP solution, although there is no form of remediation service or quarantine network capabilities. For more details, see VPN and conditional access. Define using: |
| Ability to define which management servers are accessible before user sign-in. | You can achieve this functionality in Always On VPN by using the Device Tunnel feature (available in version 1709 – for IKEv2 only) in the VPN profile combined with traffic filters to control which management systems on the corporate network are accessible through the Device Tunnel. Beijing jcz driver download for windows. Note: Define using: |
Additional functionalities
Each item in this section is a use case scenario or commonly used remote access functionality for which Always On VPN has improved functionality—either through an expansion of functionality or elimination of a previous limitation.
| Functional area | Always On VPN |
|---|---|
| Domain-joined devices with Enterprise SKUs requirement. | Always On VPN supports domain-joined, nondomain-joined (workgroup), or Azure AD–joined devices to allow for both enterprise and BYOD scenarios. Always On VPN is available in all Windows editions, and the platform features are available to third parties by way of UWP VPN plug-in support. Note: |
| Support for both IPv4 and IPv6. | With Always On VPN, users can access both IPv4 and IPv6 resources on the corporate network. The Always On VPN client uses a dual-stack approach that doesn't specifically depend on IPv6 or the need for the VPN gateway to provide NAT64 or DNS64 translation services. |
| Support for two-factor or OTP authentication. | The Always On VPN platform natively supports EAP, which allows for the use of diverse Microsoft and third-party EAP types as part of the authentication workflow. Always On VPN specifically supports smart card (both physical and virtual) and Windows Hello for Business certificates to satisfy two-factor authentication requirements. Also, Always On VPN supports OTP through MFA (not supported natively, only supported on third-party plugins) by way of EAP RADIUS integration. Define using: |
| Support for multiple domains and forests. | The Always On VPN platform has no dependency on Active Directory Domain Services (AD DS) forests or domain topology (or associated functional/schema levels) because it doesn't require the VPN client to be domain joined to function. Group Policy is therefore not a dependency to define VPN profile settings because you do not use it during client configuration. Where Active Directory authorization integration is required, you can achieve it through RADIUS as part of the EAP authentication and authorization process. |
| Support for both split and force tunnel for internet/intranet traffic separation. | You can configure Always On VPN to support both force tunnel (the default operating mode) and split tunnel natively. Always On VPN provides additional granularity for application-specific routing policies. Note: Define using: VPNv2/ProfileName/NativeProfile/RoutingPolicyType |
| Multiple protocol support. | Always On VPN can be configured to support SSTP natively if Secure Sockets Layer fallback from IKEv2 is required. Note: |
| Connectivity Assistant to provide corporate connectivity status. | Always On VPN is fully integrated with the native Network Connectivity Assistant and provides connectivity status from the View All Networks interface. With the advent of Windows 10 Creators Update (version 1703), VPN connection status and VPN connection control for User Tunnel are now available through the Network flyout (for the Windows built-in VPN client), as well. |
| Name resolution of corporate resources using short-name, fully qualified domain name (FQDN), and DNS suffix. | Always On VPN can natively define one or more DNS suffixes as part of the VPN connection and IP address assignment process, including corporate resource name resolution for short names, FQDNs, or entire DNS namespaces. Always On VPN also supports the use of Name Resolution Policy Tables to provide namespace-specific resolution granularity. Note: Define using: |
Next steps
